Level-1 Security: The Foundation of Designing Next-Generation Identity Documents
Designing next-generation identity documents requires more than layering security features. It requires structured engineering decisions that balance optical security, structural integrity, personalization technologies, and forensic resilience.
The main objective is to create a technological barrier high enough to discourage both counterfeiting and forgery attempts, while maintaining a design that is clear, appealing, and trusted by citizens.
Authentication must operate across three inspection levels:
- Level 1 (naked eye / frontline inspection)
- Level 2 (simple tools – magnifier, UV, coaxial light)
- Level 3 (forensic laboratory analysis)
However, the core level we want to focus on here is level 1, as it is often the most critical and important during inspection.
Although the electronic component is essential for biometric authentication, it will not be addressed in detail in this article, as it does not belong to Level-1 security features
The 4 Pillars of Effective Level-1 Design
1. Ease of document authentication (for any expert and non- expert):
During an inspection, officers and private inspectors often have only a few seconds to authenticate an identity document. In many everyday situations within the private sector, such as healthcare services, banking, real estate transactions, or vehicle purchases, documents are checked by individuals who may not have specialized expertise or dedicated tools.
For this reason, it is essential to integrate strong Level-1 security features that allow quick and intuitive authentication.
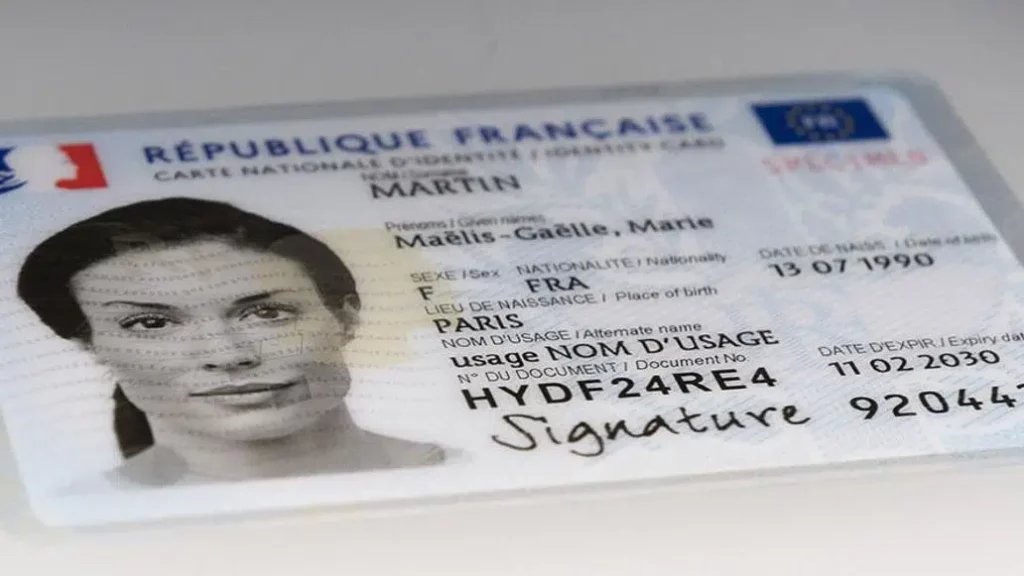
2. Ease of holder recognition (for expert and non- expert):
The portrait remains the most targeted element in forgery attempts, while it is also the primary reference used to verify the identity of the document holder.
Portrait protection must be multi-layered and redundant, using several complementary technologies to secure the link between the document and its legitimate holder.
3. Ease of detecting counterfeit
Counterfeit documents typically reveal themselves through missing, altered, or poorly replicated Level-1 security features. These visual elements are based on advanced security technologies and production expertise, making them difficult to reproduce or imitate.
By integrating strong and easily security features, inspectors—and even non-experts—can quickly identify inconsistencies that indicate a counterfeit document.
4. Ease of detecting forgeries
Forgery attempts usually target specific elements such as the portrait or variable data. These attacks often leave localized degradation or visible alterations around the manipulated areas.
Protecting these critical elements with robust Level-1 security features makes such attacks easier to detect and helps ensure the authenticity of the document and its data.
Design principles for new modern identity documents
1. Ease of document authentication:
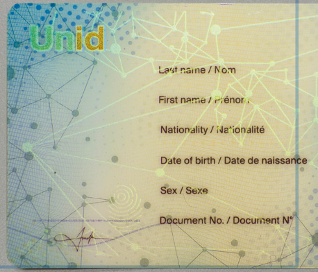
Full face embedded transparent Optically Variable feature:
Large-area optically variable elements increase intuitive verification and raise replication complexity. Placement over the whole surface, including primary portrait, enhances protection against photo substitution and data alteration.
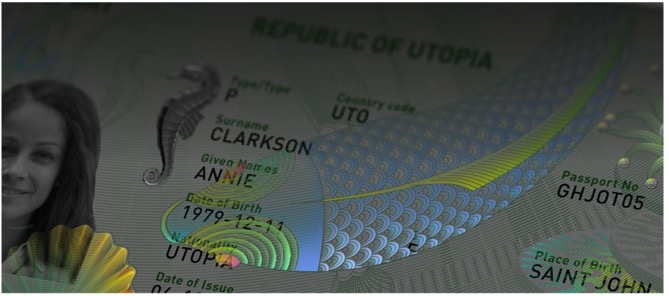
Window Structures:
Complex window designs integrating transparent color-shifting effects combine structural integrity with strong optical security features. This significantly reduces the risk of simple punched-window counterfeits with lack of optical variable elements.
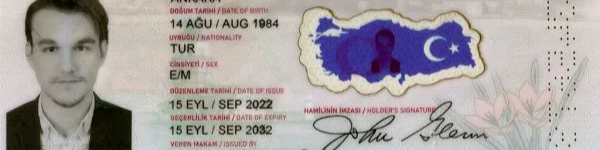
Half-window constructions exposing electronic modules and/or security features:
Half-window designs add an additional manufacturing security layer, as they require very specific industrial know-how. Controlled visibility of antenna or security features optically variable increases counterfeit detection and reinforces the authenticity of the polycarbonate architecture

Dynamic color-shifting inks in Front or Back side:
An evolution of traditional OVI technology, Pigments of the magnetic ink produces dynamic visual effects under tilt, enabling rapid and intuitive Level-1 authentication. The magnetic alignment of pigments during printing creates structured optical movement that is difficult to replicate without specialized equipment and expertise.

Embossing/tactile features on surface:
Complex embossing and tactile designs applied over personalized data, including the portrait, support intuitive tactile inspection during document control. These relief elements make it easier to detect counterfeiting or forgery attempts, particularly when a laminated overlay carrying a replacement portrait is applied to the surface, as the original tactile features become flattened, hidden, or inconsistent. They also help reveal mechanical attacks such as scratching or abrasion attempts used to reach the portrait layer, as these operations typically degrade or destroy the original embossing patterns
Secured back side of the document with full face transparent security pattern:
Full-face backside optically variable elements reduce vulnerability to rear-side delamination or abrasion attacks targeting the portrait and personalization layers, while also enabling quick tilt-based authentication during inspection.
2. Ease of holder recognition:
High Definition Main portrait:
The main portrait, embedded in the core of the card (black & white or color laser engraving), prevents substitution attempts from the surface using different personalization technologies or additional substrates.
Portrait replication options (at least 3 replications are recommended):
Moiré portrait: easy to integrate and verify visually, nevertheless basic technology
ICI, Letterscreen portraits: Intuitive authentication and highly resistant to replication or alteration.
Large efficient CLI/MLI switching images: combine personalization and embossing, therefore strong against forgeries and counterfeiting.
Portrait inside large transparent sophisticated window: Highly unique and secure; combines optical and structural security to resist counterfeiting.
Colored Portrait printed on a third page in the case of passports: Easy to implement; allows efficient comparison with the embedded portrait and the holder’s face.
Laser colored embedded portrait: very strong technology against available substitution technologies
3. Detecting Counterfeit
- Missing transparent Optically Variable element or different design/ imitation
- Simple transparent window without color change
- No half window and no visibility of electronics
- Poor or ineffective dynamic color-shifting inks performance
- Missing embossing features or incorrect design
- Poor or ineffective replicated portraits
4. Detecting Forgeries
- Optically Variable element missing or much less bright over the main portrait area and variable data.
- Embossing weakened or erased at the portrait location
- Backside full-face security patterns missing or damaged due to rear-side attacks attempting to reach the portrait layer
- Poor quality or inconsistent replicated portraits, as modifying the main portrait also requires reproducing secondary portraits produced by different personalization technologies
Conclusion
Next-generation identity documents must combine advanced security technologies that are both intuitive to authenticate and extremely difficult to replicate or imitate. At the same time, they must continuously evolve to remain resilient against emerging counterfeiting and forgery techniques.
However, designing modern documents does not mean simply adding every possible security feature. Instead, each interaction with the document—whether moving, tilting, rotating, or shifting it—should reveal clear and intuitive security cues that allow inspectors and third parties to quickly understand and authenticate the document.
Achieving this level of innovation is only possible through continuous and significant investment in research and development by industry suppliers. As a result, some advanced security features may initially be exclusive or proprietary, reflecting new technological breakthroughs. This can sometimes make open competition more complex for certain features, but it also drives innovation and enables the introduction of new levels of protection for identity documents.